What makes our solution a perfect fit for your needs?
Endpoint protection
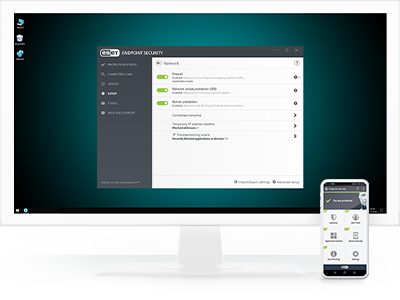
ESET Endpoint Security
Leverages a multilayered approach that utilizes multiple technologies in dynamic equilibrium to constantly balance performance, detection and false positives, enabling organizations to:
- Protect against ransomware
- Block targeted attacks
- Prevent data breaches
- Stop fileless attacks
- Detect advanced persistent threats
- Mobile protection and MDM
Try Before you Buy
See interactive demo or start a free trial
Explore ESET Endpoint Security features
Managed from a unified console
All ESET endpoints, including endpoints and mobiles, can be managed from our cloud-based unified management console ESET PROTECT.
Stop fileless attacks
ESET endpoint protection platforms have mitigations in place to detect malformed or hijacked applications to protect against fileless attacks.
Block targeted attacks
ESET’s endpoint protection solutions use threat intelligence information based on their global presence to prioritize and effectively block the newest threats prior to their delivery anywhere else in the world.
Safeguard the web browser
Designed to protect an organization’s assets with a special layer of protection that focuses on the browser, as the main tool used to access critical data inside the intranet perimeter and in the cloud.
Network Attack Protection
ESET Network Attack Protection improves detection of known vulnerabilities on the network level.
Botnet Protection
ESET Botnet Protection detects malicious communication used by botnets, and at the same time, identifies the offending processes.
Endpoint protection
ESET Endpoint Security
Managed from a unified console
All ESET endpoints, including endpoints and mobiles, can be managed from our cloud-based unified management console ESET PROTECT.
Block targeted attacks
ESET’s endpoint protection solutions use threat intelligence information based on their global presence to prioritize and effectively block the newest threats prior to their delivery anywhere else in the world. In addition, our solutions feature cloud-based updating to respond quickly in the case of a missed detection without having to wait for a regular update.
Network Attack Protection
ESET Network Attack Protection improves detection of known vulnerabilities on the network level.
Machine learning
All ESET Endpoint products currently use machine learning in conjunction with all of our other defense layers and have done so since 1997. Specifically, machine learning is used in the form of consolidated output and neural networks. For an in-depth inspection of the network, admins can turn on the special aggressive machine learning mode that works even without an internet connection.
Ransomware Shield
An additional layer protecting users from ransomware. Our technology monitors and evaluates all executed applications based on their behavior and reputation. It is designed to detect and block processes that resemble ransomware behavior.
UEFI Scanner
ESET is the first endpoint security provider to add a dedicated layer into its solution that protects the Unified Extensible Firmware Interface (UEFI). ESET UEFI Scanner checks and enforces the preboot environment’s security and is designed to monitor the integrity of the firmware. If modification is detected, it notifies the user.
Exploit Blocker
ESET Exploit Blocker monitors typically exploitable applications (browsers, document readers, email clients, Flash, Java and more), and instead of just aiming at particular CVE identifiers, it focuses on exploitation techniques. When triggered, the threat is blocked immediately on the machine.
Stop fileless attacks
ESET endpoint protection platforms have mitigations in place to detect malformed or hijacked applications to protect against fileless attacks. Dedicated scanners were also created to constantly check memory for anything suspicious.
Safeguard the web browser
Designed to protect an organization’s assets with a special layer of protection that focuses on the browser, as the main tool used to access critical data inside the intranet perimeter and in the cloud. Secure Browser provides enhanced memory protection for the browser process, coupled with keyboard protection, and lets admins add URLs to be protected by it.
Botnet Protection
ESET Botnet Protection detects malicious communication used by botnets, and at the same time, identifies the offending processes. Any detected malicious communication is blocked and reported to the user.
In-product Sandbox
ESET’s in-product Sandbox assists in identifying the real behavior hidden underneath the surface of obfuscated malware.
Behavioral Detection – HIPS
ESET’s Host-based Intrusion Prevention System (HIPS) monitors system activity and uses a pre-defined set of rules to recognize and stop suspicious system behavior.
Advanced Memory Scanner
ESET Advanced Memory Scanner monitors the behavior of a malicious process and scans it once it decloaks in memory. Fileless malware operates without needing persistent components in the file system that can be detected conventionally. Only memory scanning can successfully discover and stop such malicious attacks.